“Masque attack” could expose the bank details, emails, and other sensitive data.
Security researchers have warned of a security hole in Apple’s iOS devices that could allow attackers to replace legitimate applications with booby traps, an exploit that could expose passwords, emails or other sensitive user data.
The attack “Masque”, as described by researchers at security firm Fire Eye, is based on the supply of the company to replace banking, email, or other legitimate applications already installed on a proprietary telephone created by a malicious adversary. From there, the attacker can use the Access application sends malicious emails, tokens login credentials or other data belonging to the legitimate application.
“The Masque attacks can replace real applications, such as banking and email applications, the use of malware attacker on the Internet,” the researchers wrote in a blog Fire Eye released Monday. “That means the attacker can steal banking credentials from users by replacing a real banking application with malware that has the same user interface. Surprisingly, malware can still access local data of the original application, was not removed when the original application is replaced. These data can contain cached emails or login-tokens that malware can use to log into the user account directly. ”
The attack works by presenting a specific phone with the same type of digital certificate from large corporations use to install custom applications on iPhones and iPads for employees, provided that both the legitimate application and malicious application use the same packet identifier. The attack requires some sort of decoy to fool a goal in installing the malicious application, possibly billed as an update out of band or track to an already installed application. Recently, researchers found evidence of attacks may be circulating online, said without elaborating. The technique does not work with pre-installed iOS apps like Mobile Safari. Fire Eye researchers said they reported the vulnerability to Apple in July.
“By leveraging Masque attack, an attacker can trick a victim to install an application with a misleading name crafted by the attacker (like New Angry Bird) and the iOS system will be used to replace a legitimate application with the same identifier package “Monday’s report said.”Attack Masque could not replace own applications platform as Apple Mobile Safari, but you can replace the installed applications from the App Store.” From there, attackers can:
Imitate interface logon application replaced to steal login credentials victims
Local caches application data assigned to replace to steal access emails, Session Tokens or other sensitive data
Install custom programming interfaces are not approved by Apple on phones of victims
Skip the normal architecture built into iOS application sandbox and get root access by exploiting known possibly iOS, such as those recently conducted by the team of Pangu vulnerabilities.
Fire Eye researchers documented the following example attack proof of concept:
In one of our experiments, we used an application on the company with a packet identifier “com.google.Gmail” with a title “New Flappy Bird.” We signed this application from a certified company. When you install this application from a web page, which replaced the original Gmail app on the phone.
Figure 1 illustrates this process. Figure 1 (a) (b) show the genuine Gmail application installed on the device with 22 unread e-mails. Figure 1 (c) shows that the victim was lured to install an application on the local called “New Flappy Bird” of a site. Note that “New Flappy Bird” is the title of this application and the attacker can set it to an arbitrary value in the preparation of this application. However, this application has a packet identifier “com.google.Gmail”.
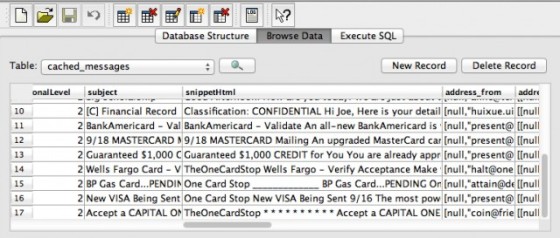
After the victim clicks on “Install”, Figure 1 (d) shows the application of the house was replacing the original Gmail app during installation. Figure 1 (e) shows that the original Gmail app was replaced by the application in the enterprise. After the installation, open the new “Gmail” application the user is automatically registered with almost the same user interface except for a small text box at the top that says “yes, you are pwned” which designed to easily illustrate the attack. Attackers will not be displayed as a courtesy to real-world attacks. Meanwhile, the emails stored in the local cache authentic original Gmail application, which were stored in plain text in a sqlite3 database as shown in Figure 2, are loaded into a remote server.
Note that Attack Masque completely passing over the wireless network, without relying on connecting the device to a computer.
Message Monday comes a few days after researchers discovered a Palo Alto Networks active malware campaign also abused company certificates to install unwanted apps on iPhones & iPads. The post FireEye WireLurker described as a “limited form of attacks Masque to attack iOS devices via USB. Attacks Masque can be a lot bigger than WireLurker threat.”
The attacks can be prevented by installing only the applications that come from official App Store of Apple. Users who encounter dialogs third party websites requesting permission to update existing applications or install new ones should be especially suspect. Users must promptly uninstall all applications that return a warning saying that “Untrusted App Developer.”